Web-Skimming attack affects 20,000 Customers on Home Improvement Site - RapidSpike

Beneath the surface: Uncovering the shift in web skimming

Ransom Monetization Rates Fall to Record Low Despite Jump In Average Ransom Payments
MAKE, Free Full-Text

All You Need to Know About Web Skimming Attacks

Magecart Archives - RapidSpike

Web Skimming Attacks - Digital Hacking Techniques for Payment Card” - Kratikal Blogs

RapidSpike on LinkedIn: Website Monitoring and Web Performance Monitoring
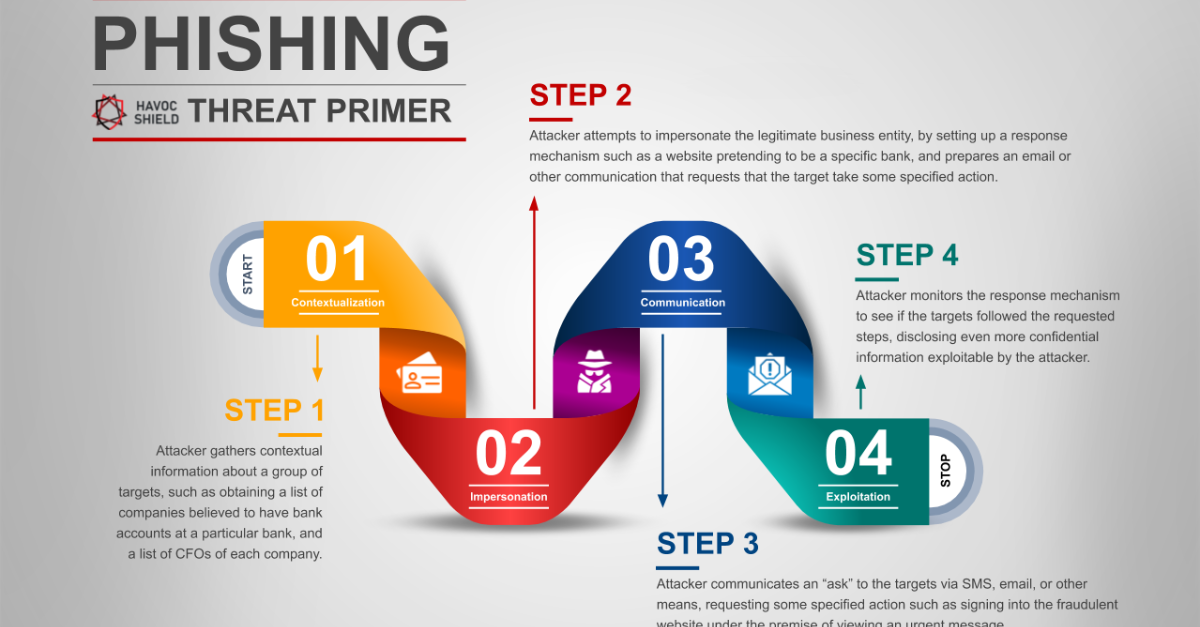
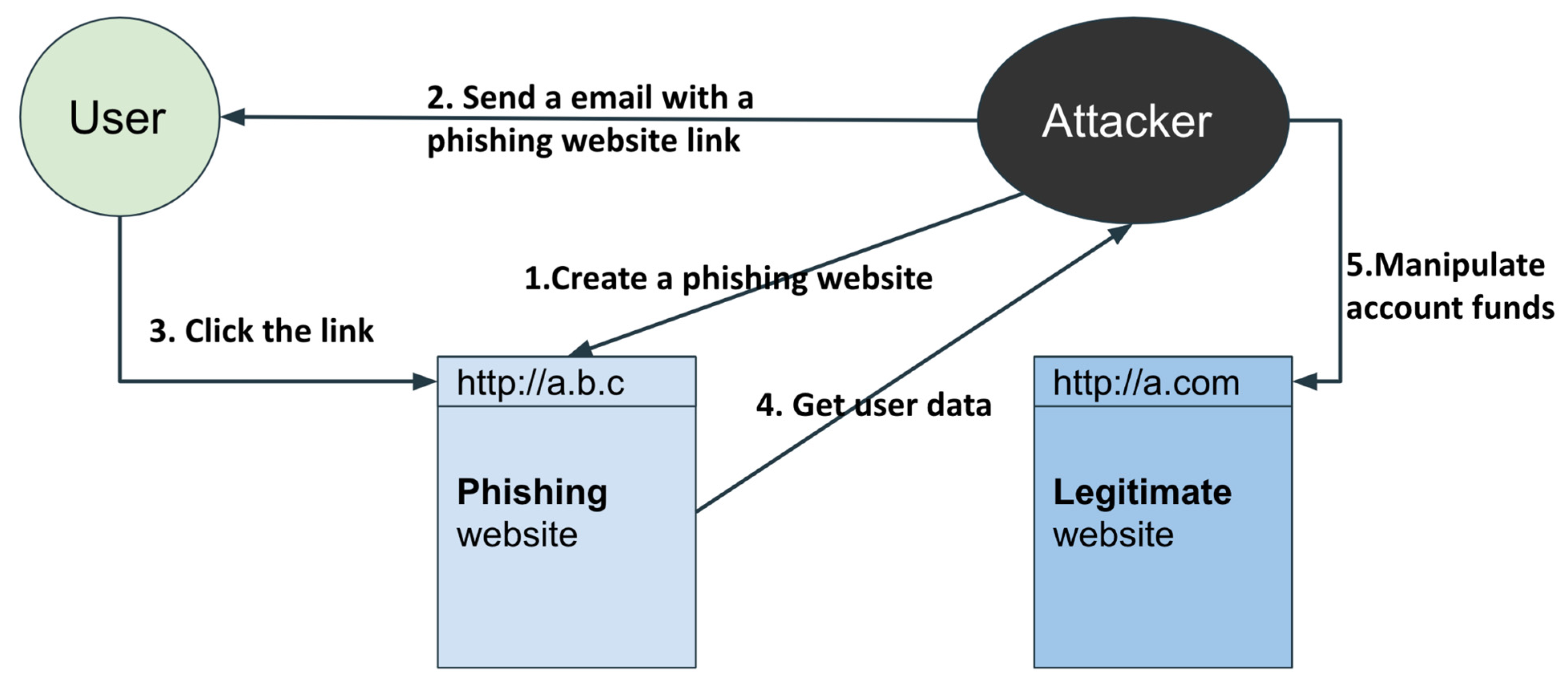
4 Phishing Steps that Cyber Criminals Use Against You

Scraping Attacks: Compromising Web Security, Impacting Business Continuity - Security Boulevard

What is Web Skimming Attacks?

Beneath the surface: Uncovering the shift in web skimming

What is Magecart Attack? ⚔️ How to prevent it?

Web skimming attacks on hundreds of real estate websites deployed via cloud video hosting service

Top 5 Web Attacks and Ways to Handle Them — Part 2

E-skimming Attacks and Client-side Security