How Hackers Use Binary Padding to Outsmart Sandboxes

Boosting Morale in the Security Operations Center with AI Analysts

Emre KISA posted on LinkedIn
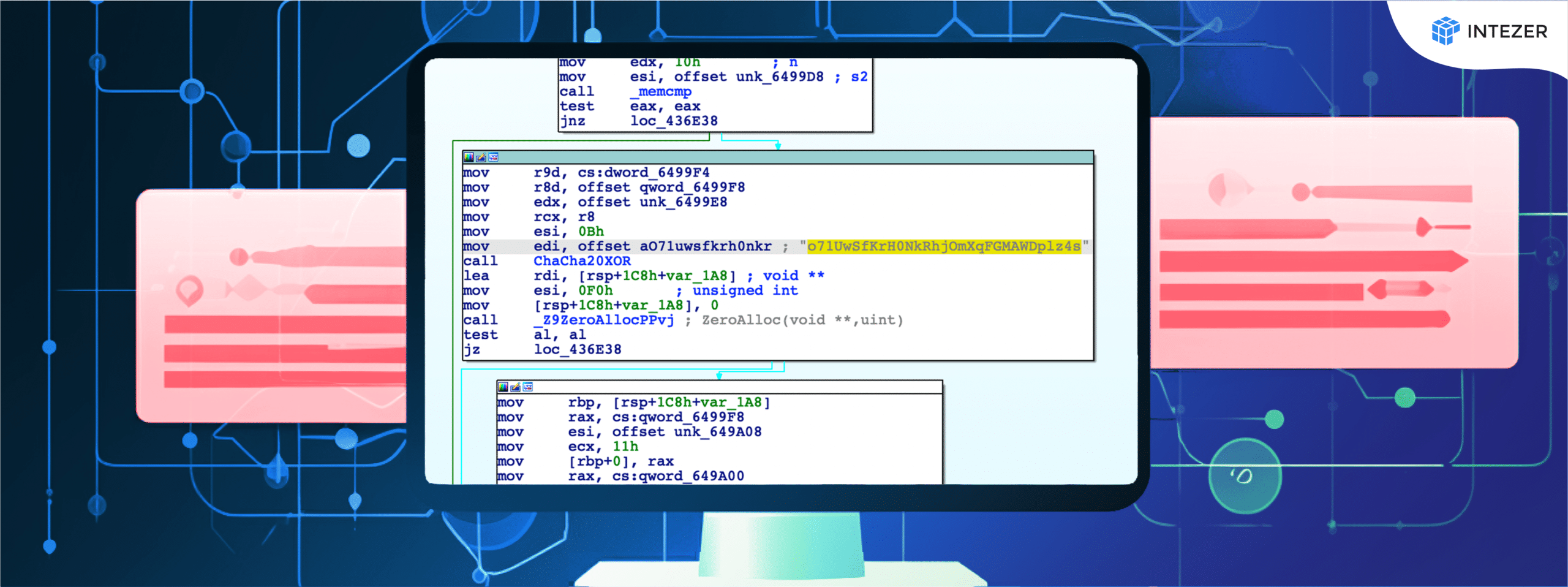
Unraveling the Secrets of Encryption in Malware

Cybersecurity News

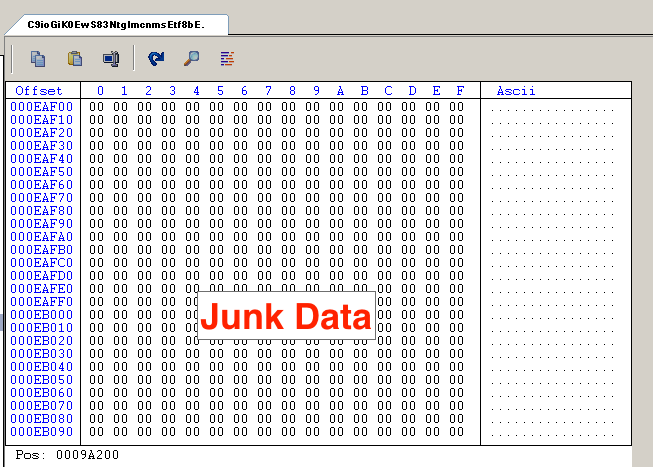
How Hackers Use Binary Padding to Outsmart Sandboxes

Optimizing Pairing-Based Cryptography: Montgomery Multiplication in Assembly, NCC Group Research Blog
Top 10 Linux Server Hardening and Security Best Practices - Intezer

CryptoClippy Evolves to Pilfer Even More Financial Data

Kaiji Goes Through Update but Code Reuse Detects It- Intezer

Emre KISA on LinkedIn: Indirect prompt injection, have you heard

Emre KISA on LinkedIn: Check out this job at Emirates NBD: Infosec