How to Choose a Secret Scanning Solution to Protect Credentials in Your Code - Spectral
Can your organization afford a data breach? If maintaining credential security is your responsibility you want to pick a good secret scanner
Top 9 Secret Management Tools for 2022 - Security Boulevard

Secrets Detection by Sonar

9 Code Scanning Tools (Small Biz and Enterprise DevSecOps)
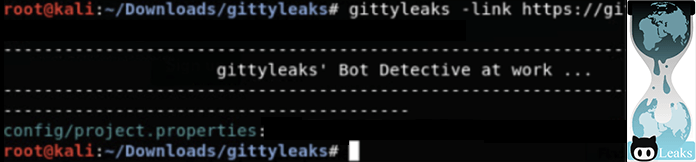
Top 9 Git Secret Scanning Tools for DevSecOps - Spectral

9 Code Scanning Tools (Small Biz and Enterprise DevSecOps)
Configure TOTP Two-Factor Authentication: /Documentation
GitHub brings free secret scanning to all public repos

IBM Spectrum Virtualize and Multi-Factor Authentication, by Ole Kristian Myklebust

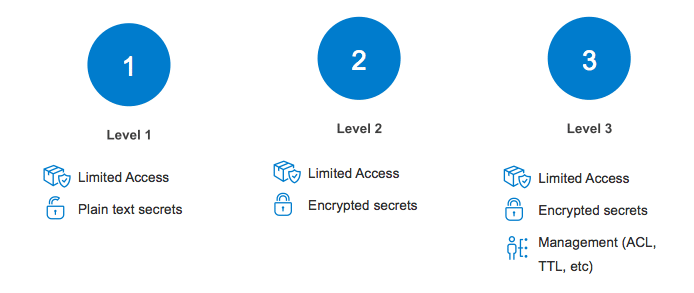
The Essential Guide to Secrets Scanning

What is Container Scanning?: Easy Guide 101 - Pingsafe Blog
Introducing Secret Validation - Cycode

Secrets Exposed: How to mitigate risk from secrets leaks — and prevent future breaches