Attackers can force Echos to hack themselves with self-issued commands

Popular “smart” device follows commands issued by its own speaker. What could go wrong?

2023 IJCAI YES inaugurated at ECNU With Keynote Speeches about the field of AI-East China Normal University

Echo security loophole exploited to make them hack themselves
REvil ransomware supply chain attack against MSPs

API security, vulnerabilities and common attacks

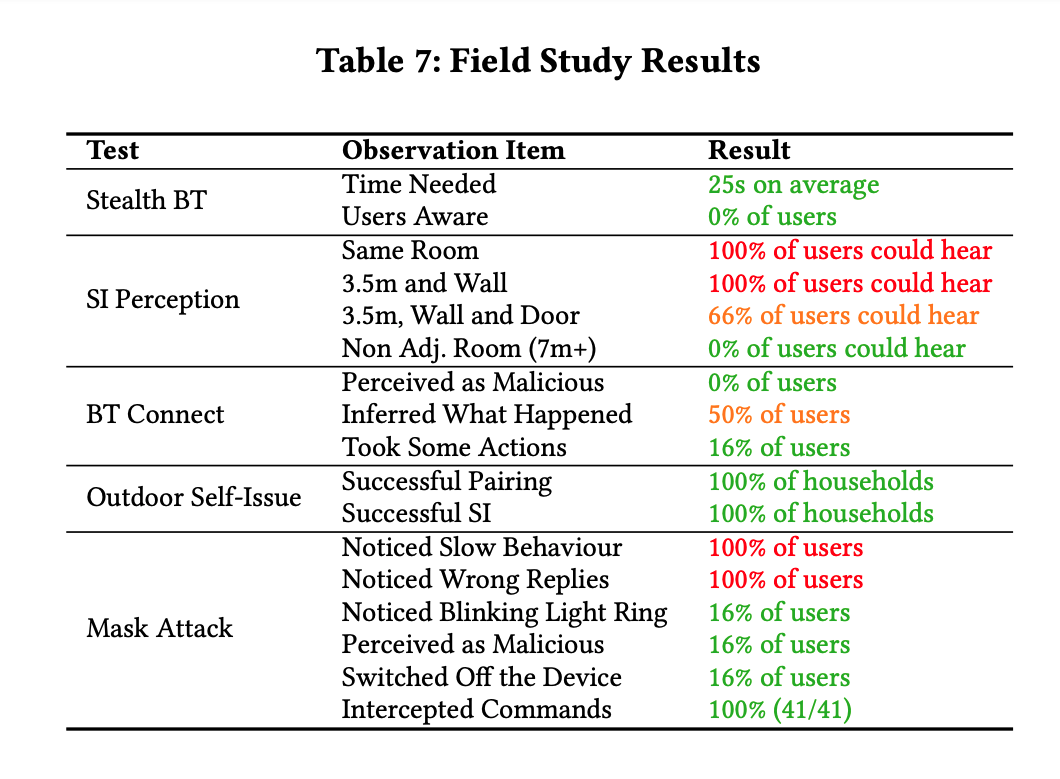
A survey on security analysis of echo devices - ScienceDirect

Computer Systems Security: Planning for Success

Cyber Risk Leaders Magazine - Issue 7, 2022 by MySecurity Marketplace - Issuu

Attackers can force Echos to hack themselves with self-issued commands
Attackers can force Echos to hack themselves with self-issued commands

A survey on security analysis of echo devices - ScienceDirect